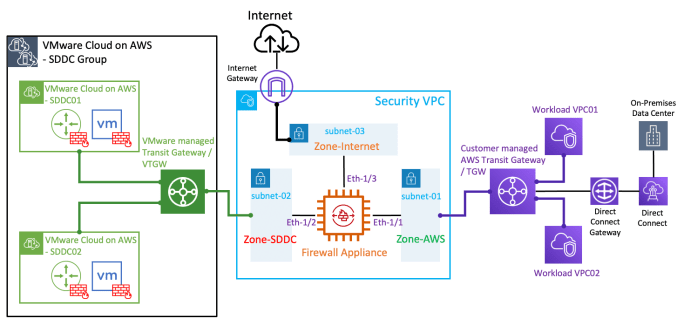
With the latest "Transit VPC" feature in the VMware Cloud on AWS (VMC) 1.12 release, you can now inject static routes in the VMware managed Transit Gateway (or VTGW) to forward SDDC egress traffic to a 3rd-party firewall appliance for security inspection. The firewall appliance is deployed in a Security/Transit VPC to provide transit routing … Continue reading Integrating a 3rd-party firewall appliance with VMware Cloud on AWS by leveraging a Security/Transit VPC