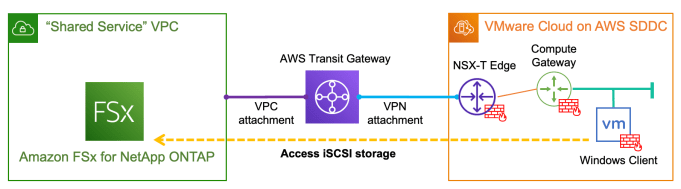
With the recently announced Amazon FSx for NetApp ONTAP, it is very exciting that for the first time we have a fully managed ONTAP file system in the cloud! What's more interesting about this service is that we can now deliver high-performance block storage to the workloads running on VMware Cloud on AWS (VMC) through … Continue reading Provision and integrate iSCSI storage with VMware Cloud on AWS using Amazon FSx for NetApp ONTAP
Category: AWS
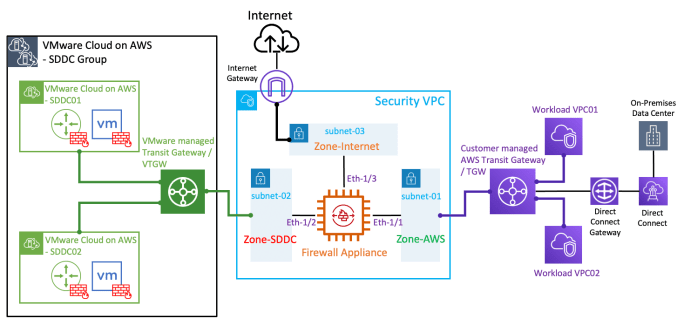
Integrating a 3rd-party firewall appliance with VMware Cloud on AWS by leveraging a Security/Transit VPC
With the latest "Transit VPC" feature in the VMware Cloud on AWS (VMC) 1.12 release, you can now inject static routes in the VMware managed Transit Gateway (or VTGW) to forward SDDC egress traffic to a 3rd-party firewall appliance for security inspection. The firewall appliance is deployed in a Security/Transit VPC to provide transit routing … Continue reading Integrating a 3rd-party firewall appliance with VMware Cloud on AWS by leveraging a Security/Transit VPC
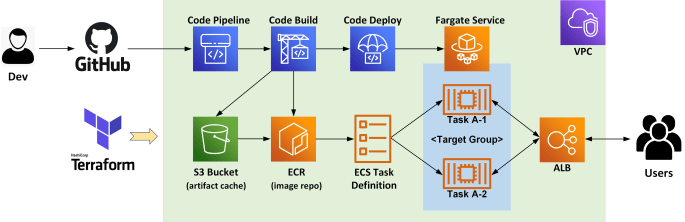
Build a Serverless CI/CD pipeline on AWS with Fargate, CodePipeline and Terraform
This blog provides an example for deploying a CI/CD pipeline on AWS utilising the serverless container platform Fargate and the fully managed CodePipeline service. We'll also use Terraform to automate the process for building the entire AWS environment, as shown in the below diagram. Specifically, we'll be creating the following AWS resources: 1x demo VPC … Continue reading Build a Serverless CI/CD pipeline on AWS with Fargate, CodePipeline and Terraform
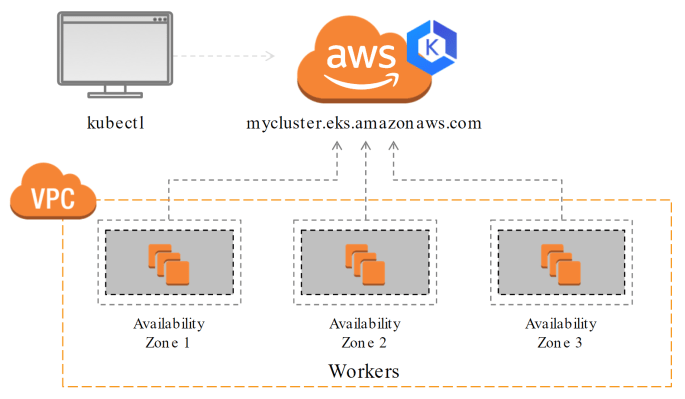
Provision an AWS EKS Cluster with Terraform
In this post we'll provision an AWS Elastic Kubernetes Service (EKS) Cluster using Terraform. EKS is an upstream compliant Kubernetes solution that is fully managed by AWS. I have provided a sample Terraform script at here. It will build a multi-AZ EKS cluster that looks like this: Specifically, we'll be launching the following AWS resources: … Continue reading Provision an AWS EKS Cluster with Terraform