This will be a quick blog to demonstrate how to enable the (embedded) Harbor Image Registry in vSphere 7 with Kubernetes. Harbor was originally developed by VMware as a enterprise-grade private container registry. It was then donated to the CNCF in 2018 and recently became a CNCF graduated project. For this demo, we'll activate the … Continue reading Enabling embedded Harbor Image Registry in vSphere 7 with Kubernetes
Category: VMware
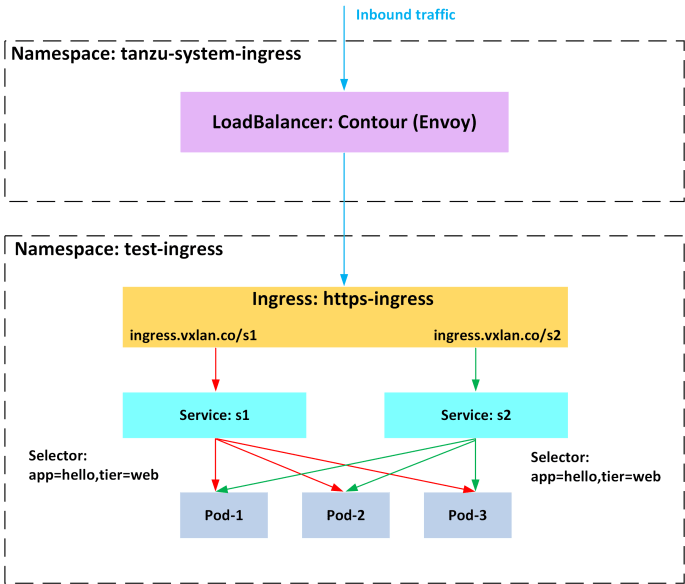
Deploying Contour Ingress Controller on Tanzu Kubernetes Grid (TKG)
This blog provides a guide to help you deploying Contour Ingress Controller onto a Tanzu Kubernetes Grid (TKG) cluster. Contour is an open source Kubernetes ingress controller that exposes HTTP/HTTPS routes for internal services so they are reachable from outside the cluster. Like many other ingress controllers, Contour can provide advanced L7 URL/URI based routing … Continue reading Deploying Contour Ingress Controller on Tanzu Kubernetes Grid (TKG)
Deploying vSphere 7 with Kubernetes and Tanzu Kubernetes Grid (TKG) Cluster
In this post we'll explore the vSphere 7 with Kubernetes capabilities and the detailed deployment steps in order to provision a vSphere supervisor cluster and a Tanzu Kubernetes Grid (TKG) cluster. If you are new to vSphere 7 and Tanzu Kubernetes, below are some background readings that can be used as a good start point: … Continue reading Deploying vSphere 7 with Kubernetes and Tanzu Kubernetes Grid (TKG) Cluster