With the recent release of VMware Cloud on AWS SDDC version 1.18, we have introduced a ton of advanced networking capabilities which opened up possibilities for many new interesting use cases. Customers can now utilise the NSX Manager UI (or VMC Policy API) to configure route aggregation at each SDDC level, and this provides an … Continue reading Integrate F5 Load Balancers into VMware Cloud on AWS SDDC Environment
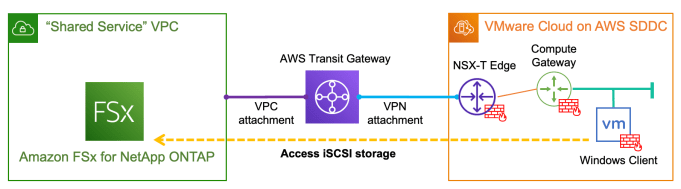
Provision and integrate iSCSI storage with VMware Cloud on AWS using Amazon FSx for NetApp ONTAP
With the recently announced Amazon FSx for NetApp ONTAP, it is very exciting that for the first time we have a fully managed ONTAP file system in the cloud! What's more interesting about this service is that we can now deliver high-performance block storage to the workloads running on VMware Cloud on AWS (VMC) through … Continue reading Provision and integrate iSCSI storage with VMware Cloud on AWS using Amazon FSx for NetApp ONTAP
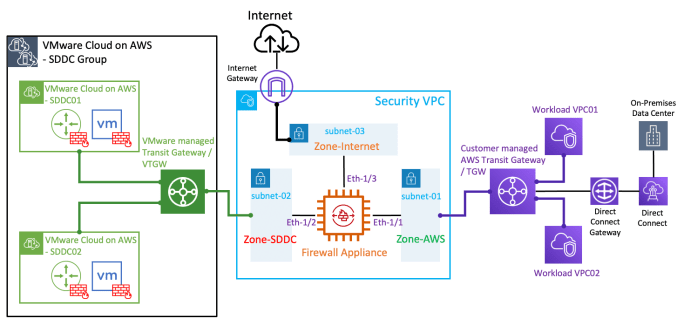
Integrating a 3rd-party firewall appliance with VMware Cloud on AWS by leveraging a Security/Transit VPC
With the latest "Transit VPC" feature in the VMware Cloud on AWS (VMC) 1.12 release, you can now inject static routes in the VMware managed Transit Gateway (or VTGW) to forward SDDC egress traffic to a 3rd-party firewall appliance for security inspection. The firewall appliance is deployed in a Security/Transit VPC to provide transit routing … Continue reading Integrating a 3rd-party firewall appliance with VMware Cloud on AWS by leveraging a Security/Transit VPC
Create a Tiny Core Linux VM Template for vSphere Lab environment
I've always wanted to find a lightweight VM template for running on nested vSphere lab environment, or sometimes for demonstrating live cloud migration such as vMotion to the VMware Cloud on AWS. Recently I have managed to achieve this by using the Tiny Core Linux distribution and it ticked all of my requirements: ultra lightweight … Continue reading Create a Tiny Core Linux VM Template for vSphere Lab environment
NSX-T Automation with Terraform
Recently I have tried out the Terraform NSX-T Provider and it worked like a charm. In this post, I will demonstrate a simple example on how to leverage Terraform to provision a basic NSX tenant network environment, which includes the following: create a Tier-1 routercreate (linked) routed ports on the new T1 router and the … Continue reading NSX-T Automation with Terraform